Get in Touch
Russian state-sponsored threat actor, Killnet, takes aim at UK organisations
Target Industry
- Government services
- Healthcare services
- Energy services
- Defence & Aerospace
- Financial services
Overview
Severity level: Medium – Exploitation may result in temporary loss of online systems.
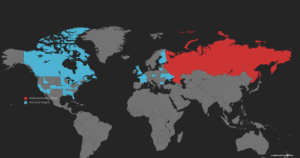
Notorious Russian state-sponsored threat group, Killnet, has threatened a wave of distributed denial of service (DDOS) attacks against UK government services and the healthcare sector, likely in response to the continued UK support to Ukraine.
In a statement made via their Telegram page, Killnet intends to target “all medical institutions, government services and online services”. The post also alludes that this wave of potential attacks is in retaliation for the recent “supply of high-precision missiles to Ukraine”.
Previous DDOS attacks by Killnet have been carried out against several US organisations including 12 state websites and 24 airport sites during the month of October, and more recently on 22nd November against Prince William’s website, that took the site down for several hours. In some additional posts, the group said it was going to attack the British Army, the Stock Exchange and the Bankers Automated Clearing System (BACS).
DDOS attacks are implemented by flooding the target network with spam internet traffic to overwhelm the target server, causing it to crash and require maintenance to restore normal service. Commonly, these attacks are carried out with the assistance of a botnet, allowing increased coordination by the attacker.
Impact
A successful DDOS attack will crash a victim’s online service, potentially for a prolonged period of time. Depending on how reliant a service is on online sales and activity, the affected business may lose a significant amount of potential financial gain.
Vulnerability Detection
Network traffic will spike dramatically and highly likely result in a temporary server crash.
Affected Products
- WindowsOS
- macOS
- Linux
Containment, Mitigations & Remediations
Microsoft Azure offers a protective service for DDOS defence.
Indicators of Compromise
No IOCs.
Threat Landscape
DDOS attacks have become increasingly prevalent post the Russian invasion of Ukraine. DDOS is now a mainstay of hybrid warfare and is commonly used to attack services and infrastructure deemed important by the opposing side. Killnet is widely reported as a Russian state-sponsored threat actor, so the spike in activity post invasion is no surprise. Future attacks will highly likely coincide with geopolitical actions between the UK and Ukraine, such as aid deliveries and overt support.
With the exception of sectors previously mentioned, critical national infrastructure such as energy companies and financial services are most likely to be targeted due to their inherent ties to the UK.
Threat Group
Killnet has voiced open support for the Russian state since the early days of the conflict in Ukraine. DDOS attacks have been their weapon of choice and have targeted multiple Western states and organisations during this time.
Mitre Methodologies
T1005 – Data from local source
T1057 – Process discovery
T1059.007 – JavaScript
T1083 – File and directory
T1486 – Data encrypted for impact
T1489 – Service stop
T1490 – Inhibit system recovery
T1498 – Network denial of service
T1498.001 – Direct network flood
T1499 – Endpoint denial of service
T1547.001 – Registry run keys / Startup folder
Further Information
Hackread – UK Threats
Hackread – European Parliament DDOS

