Get in Touch
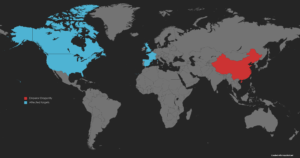
Cheerscrypt ransomware linked to Chinese state-sponsored APT
Target Industry
Previous targets have included organisations from the Financial, Construction, Advertising, and Healthcare sectors.
The Defence sector remains a potential target due to Chinese-state ambitions.
Overview
Severity level: High – This attack method is difficult to exploit, however, once successful, the exploit may result in significant sensitive data loss.
The Cheerscrypt ransomware has previously been affiliated with cyber-attacks against western private organisations and is highly likely linked to the Chinese state-sponsored group ‘Emperor Dragonfly’ also known as ‘Bronze Starlight’, based on the victims being targets of interest for the Chinese government and report correlation.
First detected in May 2022, Cheerscrypt is deployed as part of a chained attack made up of multiple malware strains including initial system exploitation by Night Sky, the deployment of a Cobalt Strike Beacon, then the post exploitation and encryption of data by the Cheerscrypt ransomware.
The chain attack targets VMware Horizon via the widely reported Log4j vulnerability (CVE-2021-44228) to execute PowerShell commands, enabling the deployment to Cobalt Strike and ultimately Cheerscypt. The technique of multiple malware swaps in a single attack is designed to confuse the defender and obfuscate the attacker’s identity.
Impact
Successful exploitation will enable attackers to breach secure networks, steal data, and encrypt devices. Data will be sold on the dark web for financial gain and to fund future attacks.
Vulnerability Detection
If compromised, detection will be obvious as data will be encrypted and a message will be displayed informing you of the breach and the attacker’s demands.
Affected Products
VMware Horizon servers on both Windows and Linux.
Containment, Mitigations & Remediations
Customers are strongly recommended to update all VMware Horizon instances to the latest patch to bring them in line with the latest defensive structure.
Additionally, customers are advised to use counter measures such as Microsoft Defender to detect and block malicious attempts and malware infiltration.
Indicators of Compromise
Known Night Sky hash:
8c1a72991fb04dc3a8cf89605fb85150ef0e742472a0c58b8fa942a1f04877b0
1fca1cd04992e0fcaa714d9dfa97323d81d7e3d43a024ec37d1c7a2767a17577
a077a55608ced7cea2bd92e2ce7e43bf51076304990ec7bb40c2b384ce2e5283
Associated Night Sky IP:
139.180.217.203
Known Cobalt Strike hash:
d78bdef2ec67cb29a28d57e1579bb6f359d3dfcd7602d64d0673311ad83edbb2
02bf021081901bb47de6253653f4021528eb30727350cc0a680d507dca723f6d
a5495ec4fab7529aa7a64a9d2aaa18f8f98752fd5523b19870c82b6dfbd80980
203ea42ca09815cd98697bed8a2734304dbc6a82f7c63b7fca7b96e066eef833
42b23dafaf9df05efbacd78b76d24668a1c74b8d6fb7695ecf871532a8bd2f4e
926397027a90be764dd2096f6072651671a872c31e9dc0c730d25d1ac5985c99
93df9db2cef5ea29dde81d7e23285f36540534369b312cc03c5b4ff198337230
b1a3d3681aaa43bd214e6d0d1d385c49784efe06a16e78f27d9ce4636fb3279f
c1f64a07f179f54506fa27878ed14a0444c494b674494dcd43e4841b7bff02ef
e9738bc8f01352fcd73645b5b67e3a23225afd5501be4ae924273926721190ac
3b2eb2f6b5e0dd40569d407b5ec50b57f041d6803ee4d543777073e4cdabf5ee
f0a56b86e2f6efa1fec4a0c090681038bd1e2597255a50375de72cacfb2392dd
6334604f7ee7686bbeb9d55dc1b4e9a0e4cfa84bae2663b243c190d0aed29e84
Associated Cobalt Strike IP:
101.42.173.185
101.43.139.124
139.155.90.81
139.224.191.217
173.82.206.56
193.239.84.150
43.132.190.156
59.110.169.75
78.128.112.215
Known Cheerscrypt hash:
e2904f5301b35b2722faf578d1f7a4d4
240118f6205effcb3a12455a81cfb1c7
2893d476408e23b7e8a65c6898fe43fa
37011eed9de6a90f3be3e1cbba6c5ab2
5a852305ffb7b5abeb39fcb9a37122ff
8161d8339411ddd6d99d54d3aefa2943
e5fd4d5774ad97e5c04b69deae33dc9e
f0656e3a70ab0a10f8d054149f12c935
51be3e3a8101bc4298b43a64540c422b
5695de561a065123178067fcedf39ce3
5a6008cf994779cde1698a0e80bb817d
c85a6814b99c8302af484563d47d9658
ea4ca87315d14f5142aaef1f5e287417
f9322ead69300501356b13d751165daa
Associated Cheerscrypt IP:
139.180.217.203
207.148.122.171
128.199.151.146
139.59.243.219
178.128.10.213
Threat Landscape
There is a realistic possibility that targeted Chinese attacks against western organisations are conducted as ransomware to mask government-sponsored espionage under a guise of financial motivation. This then moves blame away from the Chinese government and the motive of intellectual property theft.
While there are no reports of this method of attack directly targeting the defence sector, the sector is almost certainly a top priority for the Chinese government and future attacks cannot be ruled out.
Threat Group
Chinese State-Sponsored ‘Emperor Dragonfly’
Mitre Methodologies
Night Sky tactics, techniques and procedures (TTPs):
T1005 – Data from Local System
T1078 – Valid Accounts
T1486 – Data Encrypted for Impact
T1497.003 – Virtualization/Sandbox Evasion: Time Based Evasion
Cheerscrypt TTPs:
T1005 – Data from Local System
T1021.002 – Remote Services: SMB/Windows Admin Shares
T1027 – Obfuscated Files or Information
T1047 – Windows Management Instrumentation
T1048 – Exfiltration Over Alternative Protocol
T1059.001 – Command and Scripting Interpreter: PowerShell
T1059.004 – Command and Scripting Interpreter: Unix Shell
T1078 – Valid Accounts
T1190 – Exploit Public-Facing Application
T1486 – Data Encrypted for Impact
T1497 – Virtualization/Sandbox Evasion
T1567.002 – Exfiltration Over Web Service: Exfiltration to Cloud Storage
T1569.002 – System Services: Service Execution
T1570 – Lateral Tool Transfer
T1574.002 – Hijack Execution Flow: DLL Side-Loading
Further Information
Bleeping Computer – Chinese Ransomware Decoy Attacks
TechTarget – China exploiting Log4j

