The previous article on Microsoft Defender introduced the various family members. This article delves a little deeper into one of them, Microsoft Defender for Endpoint (MDE). We focus on how the product can create an automated inventory of your infrastructure. This ties in with how Microsoft is making more investment in analysing network traffic for malicious activity, an area quite new to the company who for decades have rightly advocated identity as the security perimeter.
As the new millennium chimed in some 23 years ago the market was awash with firewall vendors selling Next Generation (NG) updates of their product lines. Attacks still succeeded as this perimeter defence method was defeated by:
- Using the universal firewall bypass ports of 80 or 443
- Attempting to filter 443 (TLS encrypted comms) which was too expensive to make and break all SSL/TLS based connections
- An increasing number of devices operating outside of the corporate network; this grew as cloud services gained in popularity and employees worked remotely.
Instead, the emphasis moved to first protecting a user’s identity and then protecting the device being used to access services. Device protection is where Defender for Endpoint offers a comprehensive service. Over the last year, Defender for Endpoint has started to acquire a number of network analysis features. These are:
- Ability to listen to network broadcast traffic and interrogate certain endpoints
- Integration with Zeek, adding network analysis into Windows platforms to detect certain attack styles
- Integration with Defender for IoT to identify a broader range of devices
- Integration with Defender for Threat Intelligence to automatically label network facing devices.
Device discovery
MDE allows for device discovery primarily to find unmanaged devices that are connected to the corporate network. This discovery takes place on already MDE-enrolled Windows (10/11) machines. Anything with an IP address on the same network can be scanned. There are two methods used to scan:
- Basic discovery mode: Uses network broadcasts and nearest neighbour protocols to passively collect data on the endpoints. No network traffic is created, and the results of this passive listening are used to build up the inventory database. Under the covers SenseNDR.exe is used to monitor this broadcast traffic. This discovery mode can be disabled if required.
- Standard discovery mode: MDE-enrolled Windows endpoints can actively probe observed devices on the network. Only the endpoints observed from the passive scan above are actively probed. This mode is used to find additional information around the discovered endpoints.
The following rules are used when scanning actively or passively:
- Only MDE-enrolled machines running Windows 10 (1809+), Windows 11 or Windows Server 2019+ can run the discovery service
- The service can detect home networks (using a variety of methods) and won’t scan them by default, though this can be overruled which is useful for home lab environments
- Passive protocols in use include ARP, DHCP, CDP, LLDP, LLMNR, mDNS, SYN headers, UDP headers amongst others
- For active scanning additional protocols are used including FTP, HTTP, ICMP, RDP, SIP, SMTP, SNMP, SSH, Telnet, SMB, VNC, LDAP and even iPhone sync! This probing generates around 50Kb of network traffic per endpoint
- Typically, devices are probed once every three weeks, though there are triggers to kick off rescans to keep the inventory current
- Passive monitoring is constant
- Active scanning may trigger IDS/IPS type services. Although the probing is carried out very gently some systems may show this activity as malicious. This false positive detection should be rare as the scanning is very distributed (from multiple nodes) by design and only unmanaged devices are probed
- It is possible to exclude networks and devices from being probed
- Typically, at least two MDE-enrolled machines are needed on the subnetwork so the service correctly identifies the network as corporate as opposed to home, although these rules can be overruled in the interface
- By default, active (standard discovery) scanning is enabled for all customers.
The screenshot below shows the main device inventory data. This includes threat and vulnerability risk status, OS platform, sensor health (if enrolled), device first and last seen amongst other columns that can be configured. The screenshot below shows 479 discovered devices, 156 of which could be onboarded. Tabs exist for network devices and IoT/OT – more about these tabs later in this article.

Authenticated scans
There is a final scanning feature available which covers networking equipment and unenrolled but known Windows endpoints.
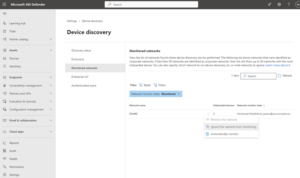
There is a download available, the screenshot below shows the ‘Authenticated scans’ option where this download can be found and installed on a dedicated machine in each subnet. There is a maximum of 40 machines running the scanning tool per tenant and they must be MDE-enrolled and running a reasonably new version of Windows. The screenshot also shows how the default settings around scanning particular networks can be overridden, in this case forcing scanning on a correctly identified home network.
Network devices
The network based operating systems that are supported include Cisco, Juniper, HPE, Palo Alto and Fortinet and the SNMP protocol is used to read information from these devices. IP addresses, authentication methods, passwords and community strings are all configured within the scanning tool.
Windows devices
Scan will run every 4 hours or once only, though this can be configured. A group managed service account is required to remotely access Windows devices that have WMI access enabled. The learn.microsoft.com pages have information on how to configure the required settings.
Zeek integration
During 2022, Microsoft re-engineered Windows to be able to integrate Zeek, an open-source network security monitoring platform, into the platform. Although full access to this new ability is yet to be released it’s already being used to detect certain attack patterns such as PrintNightmare and New Technology LAN Manager (NTLM) based password spray detections. This sets a solid foundation for the ability to detect future attacks from raw network packets received by the endpoint, rather than waiting for them to be processed by the host operating system, though this detection currently only operates on Windows devices.
There is an additional detection method, for customers already using more classical network detection systems (such as Corelight, which is also based on Zeek). It is possible to integrate alerts from a Corelight solution directly into MDE; these solutions typically have a greater amount of detail of what is happening across the network to complement host-based packet analysis.
Integration with Defender for IoT
Within the IoT tab under ‘Devices’, additional information is available if customers also have a Defender for IoT plan active and this has been enabled within the Microsoft 365 Defender dashboard. This integrates any alerts from IoT devices into the dashboard, adds additional security recommendations and discovered vulnerabilities. In effect, each MDE-enrolled Windows machine becomes a sensor for the IoT service, though a light version of full sensor that can be downloaded from the Defender for IoT service.
Integration with Defender for Threat Intelligence
A more recent integration that allows MDE to highlight (or rather tag) machines that are internet facing. This will likely be the first of many threat intelligence enrichments that use this integration, which uses successful SSH, HTTP, DNS or FTP connection requests coupled with Defender for Threat Intelligence (the old RiskIQ product) that provides an external view on internet connected resources.
Versions of Defender for Endpoint
The automated device discovery in only available as part of the Premium 2 SKU of MDE. However, it’s also part of the Defender for Vulnerability Management product as well, as under the covers this feature is part of the vulnerability management engine.
Thus, the automated discovery feature also shows vulnerability information for all discovered assets if available.
Conclusion
With some careful configuration of the features involved with device discovery and inventory, combined with some integrations, the service can give an immensely powerful automated self-discovery, self-updating device database complete with a vulnerability assessment as well. This database is stored within the standard tables that sit behind the Microsoft 365 Defender service and can be queried using Kusto Query Language (KQL) for advanced threat hunting as required. And as previously stated, the configuration out of the cloudy box now has many of these features enabled by default.















