Welcome to Part 2 in our 4 part series where we will be looking at Email Security Hardening by setting up SPF, DMARC, DKIM and creating MailFlow rules. In Part 2, we will be focusing on DomainKeys Identified Mail (DKIM).
DomainKeys Identified Mail (DKIM) is a form of Content Authorisation Protocol and is used to verify that the author of a message is sending from the domain they claim to be. This is achieved by the use of asymmetric cryptography to digitally sign portions of the header (however the body can also be signed, but this is less common) of an email.
Similar to SPF, a DKIM entry is published in the DNS record as a TXT entry and holds the encryption mean utilized and the public key that can be used to decrypt messages to the corresponding private key that is generated when DKIM is setup. DKIM provides a cryptographic signature of portions of the email’s header and recipients of messages sent by the domain in question can use the published public key to decrypt messages signed with the domain private key to verify it was indeed sent by the domain.
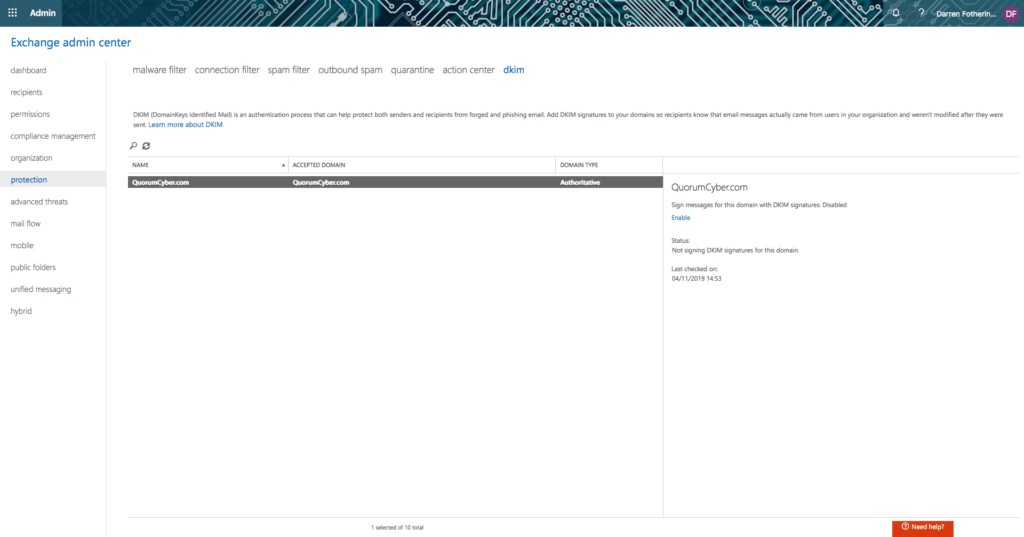
The setup process for DKIM varies depending on your mail provider, however, for Microsoft 365 environments it can be applied via:
- Exchange Admin Centre
- Protection
- DKIM
- Select your domain
- Enable
You will find that this fails, and Microsoft will recommend 2 CNAME lines which need to be added to your DNS record before you can proceed. These lines should appear similar to:
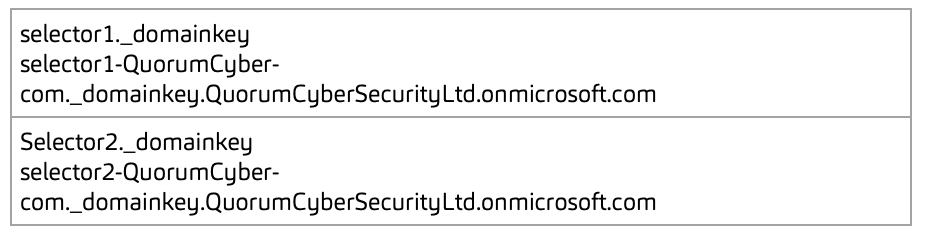
These CNAME entries should be added to your DNS record using the same method discussed to add the SPF record, however the Type should be CNAME rather than TXT, the host name/alias would be:
selector1._domainkey and the address to point to selector1-QuorumCyber- com._domainkey.QuorumCyberSecurityLtd.onmicrosoft.com.
This should also be repeated for selector2.
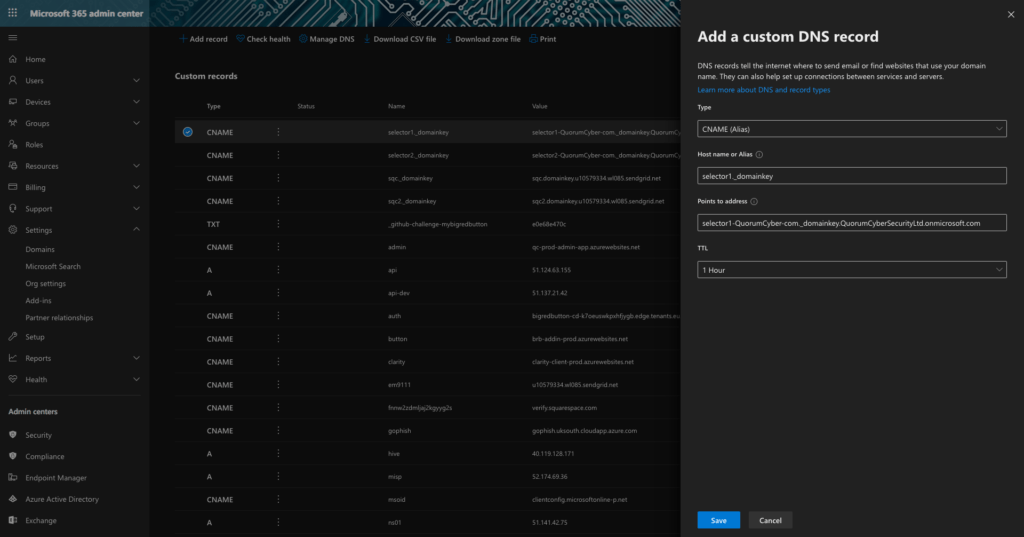
There will be a difference of course between the above and your own CNAME entries recommended by Microsoft, but these should primarily be changing the mentions of Quorum Cyber to your own domain and the first com entry to match your own top-level domain (com, co-uk, net, org, etc). Once these 2 CNAME entries have been inputted you may find you need to wait up to 24 hours (however typically less than 60 minutes is actually required) before attempting to enable DKIM again as the CNAME entries can take some time to properly propagate across the Microsoft infrastructures.
Once successfully enabled you will find that emails sent will now be signed by you DKIM policy.
Common Mistakes
Incorrect syntax/content
The rules regarding SPF/DKIM/DMARC contents in your DNS record are fairly rigid, specific tags must be included as well as a series of optional tags for more granular control. However, outside this, any additions/notations/etc may cause the policy to fail due to errors in how it is interpreted. This also applies to the addition of unexpected information in fields, such as an email address with the SPF record. Care should be taken when adding IP ranges, as the omission of “2” in a “/32” address range, could have a significant impact.
Meet the Author
Darren Fotheringham
CSIRT Lead, Quorum Cyber 
“Since starting in cyber security, I have had a keen interest in all aspects of blue team and working with new technologies to investigate potential threats on behalf of our customers. With such a diverse field of study, there is always something new to learn or defend against, and this challenge of continual progression makes every day feel new and exciting.”
For further support from our expert Security Operations Centre and Professional Services teams, contact the Quorum Cyber team today.















