To borrow a phrase from the early 17th century, prevention is better than cure!
The security industry is heavily weighted to reacting to incidents once they have occurred. What if the industry could invest as much time in preventing the incident in the first place? Instead of the Security Operations Centre (SOC) working and mitigating a ticket for ransomware found on an employee’s machine, could they issue a ticket to the IT team alerting them to a configuration weakness in the employee’s device estate that could have prevented the attack?
The first obstacle on this long and varied road of prevention is finding out what an organisation is trying to protect (inventory) and how to measure the degree of prevention. The next obstacle is the environment, or rather multiple environments including on-premises, Microsoft Azure, GitHub and other cloud vendors. The table below gives an idea of which cloud providers are the most popular by market share. The point being, there exists a need to monitor all the environments within your organisation.
| Cloud Service | Percentage of market share |
| Amazon Web Services (AWS) | 34 |
| Microsoft Azure | 21 |
| Google Cloud Platform (GCP) | 11 |
| Alibaba | 5 |
| IBM | 3 |
Quorum Cyber has already started working on the prevention journey for our customers with advisory offerings and our Managed Extended Detection & Response (M-XDR) service that proactively manages the Microsoft 365 Defenders that help protect identities, devices, applications, and data.
To extend this prevention coverage into the environments above, a different approach is needed, in this case posture management, or rather Cloud Security Posture Management (CSPM). The tool of choice in this space (as a Microsoft partner) is Defender for CSPM which is part of Microsoft Defender for Cloud. It’s enjoyed some recent updates that enables it to monitor two-thirds of the commercial cloud space and additional environments as shown in the mini screenshot below (Microsoft Azure is implicit!).
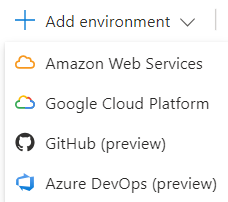
Placing the development environments to one side (they are in public preview) the key part is that Azure, AWS and GCP can all be monitored, measured and even mitigated from a single cloud dashboard.
There are two flavours of Microsoft CSPM to consider: Foundational and Defender.
Foundational CSPM
Included within Defender for Cloud by default, therefore free at point of use.
Secure score
The service will provide a list of security recommendations that can be actioned to improve an organisation’s secure score. Each environment (Azure, AWS and GCP) is scored individually to help target the priority areas for mitigation. There are many hundreds of recommendations per environment, the full list can be referenced on Microsoft’s security recommendations page.
Asset inventory
This will list the inventory of discovered assets in each environment complete with any security recommendations. It’s a fully searchable and filterable inventory that can even be exported to a CSV!
Microsoft cloud security benchmark
This represents a hybrid cloud approach, which builds up a security benchmark by adding the necessary polices into the ultimate Microsoft cloud security benchmark (MCSB). So this could be Azure Security benchmark, plus another from AWS and another from GCP to potentially give a benchmark for the entire environment.
Defender CSPM
This is a chargeable service costing around £4.20 per asset per month. An asset is classed as a server, database or storage account. It allows for the features outlined below.
Governance
An ability to set an owner for any (configurable) level of impacted recommendation and to track progress on each recommended mitigation. This can also be set by scope, as in different owners for each Azure subscription, AWS and GCP environments.
Regulatory compliance
This adds to the MCSB above with industry-aware compliance controls such as PCI DSS, SOC, HIPAA, and NIST to name a few.
Cloud security explorer
This is in public preview for GCP but general availability for Azure and AWS. It’s an ability to search through the data held by Defender for Cloud to answer specific questions from the business. Numerous templates are built in complete with the ability to build your own queries. The inbuilt templates include areas such as internet-exposed virtual machines (VMs), VMs vulnerable to a specific vulnerability and EC2 plaintext secret in play.
Attack path analysis
This identifies what an attacker may prioritise when carrying out reconnaissance against your organisation. It highlights security issues that have an immediate threat combined with a high potential of being exploited. It manages this by combing through data from the monitored assets, permissions matrix and network traffic. This feature does require agentless scanning (see below).
Agentless scanning
This feature can be split into two areas:
• Agentless VM scanning – runs every day using OS APIs across Azure, AWS and GCP for Windows and Linux. Behind the scenes it takes a snapshot of the disk and then scans this image, which is deleted after being scanned. This feature actually uses the Defender for Vulnerability Management engine to carry out the scanning.
• Agentless container scanning – will discover Kubernetes components and then provide a vulnerability assessment of all the container images with near real-time scanning of new images and daily scanning of current images. Note, this feature is currently restricted to Azure only.
Data aware security posture
This is a bigger topic of conversation but at its core allows for automatic sensitive data discovery across a range of different storage types and cloud platforms. Azure blob storage, Azure data lakes, AWS S3 buckets, RDS databases, and GCP storage buckets are all included within this feature.
Defender External Attack Surface Management (EASM)
The Defender External Attack Surface Management (EASM) isn’t so much a feature but rather an integration option. EASM is a passive scanner (it constantly scans the entire internet in the background) that can be seeded with your organisation’s identity in the form of URLs, domain names and IP ranges to see what information is available about you on the internet. This data is then used by several of the features above and can be queried via the cloud security explorer.
Summary
Defender CSPM replaces the old Defender for Cloud connectors that exist in Security Command Centre (GCP) and Security Hub (AWS) with an agentless tool for scanning, as described above. And as noted at the beginning of this article, Security Posture Management is all about prevention by discovering and then using policy and technology to protect the assets within the inventory.
This concept will continue to grow in the future. Microsoft is hinting that it will extend Security Posture Management to beyond cloud / development environments to include the other families of Defender and even third-party sources of security information. Cross Security Posture Management, also known as XSPM, will be arriving soon to add weight to the argument in investing in the prevention as well as the cure.















