If you read our earlier blog piece titled ‘Phishing Scams in the Age of COVID-19: Avoid the Traps’ you won’t be at all surprised to learn that, since the invasion of Ukraine, nefarious groups and individuals have been trying to scam people by masquerading as charities or even as official departments of the Ukrainian government.
It’s well known that scammers like to piggyback major news themes of the day and tune into the feelings and sympathies of everyday people. They take advantage of their emotions and hope to catch people out at times when they aren’t carefully and meticulously checking the authenticity of every piece of content they receive or verifying the sender behind them. Fraudsters often use emotive headlines and eye-catching topical images in their content to draw in their intended targets, who are perhaps already willing to make a donation to a worthy cause. Unfortunately, they’re trying to take advantage of donors’ good will and generosity during Europe’s largest humanitarian relief effort in decades. And while the theme is different now – replace COVID-19 with the war in Ukraine – the methods are mostly the same.
Phishing for everyone
Many fraudsters use phishing, a social engineering technique that comes in a variety of guises, including fraudulent emails, text messages, and phone calls. As we described in our article of May 2020: “Phishing is a technique where an email containing a malicious attachment or a link to a malicious website is sent to a person. The content of the message is designed to convince the user to open the attachment or provide personal details.”
Phishers target individuals, charities, government organisations, healthcare institutions and businesses of all sizes. Anyone and everyone could potentially receive such a message, whether they are using a personal or work device, regardless of what measures have been put in place to prevent them from coming through. It’s basically a numbers game – while some people will instantly spot the warning signs, others will fall for the trap. The culprits know they won’t fool everyone; they just want to trick as many as possible to hand over their money.
Cryptocurrency donations, fake identities and fake websites
Since February, genuine humanitarian relief agencies have been actively appealing for funds to save lives, to rescue, feed and shelter the millions of innocent people who have fled the country, or who are internally displaced by the conflict. And recently, to make it easier for anyone around the world to assist his country financially, Ukraine’s President Volodymyr Zelensky has written into law that the country can accept cryptocurrencies as donations to help its citizens.
Sadly, cyber criminals have been quick to jump onto this and the more sophisticated of them have made their phishing attacks look much more authentic by pretending to be real people. An investigation by the BBC discovered that a few people around the globe who have been raising funds for Ukraine online have had their identities stolen and their social media accounts hacked or cloned. Consequently, much-needed donations have been diverted away from the people who really need them into criminals’ accounts.
According to the BBC, fake emails vary from those pretending to be from UNICEF to pleas for help from someone claiming to be the director of a children’s hospital in Ukraine.

Example of a red cross fake email.
Source: Reddit
And they report that fake websites have been set up to look like trustworthy charitable organisations including The British Red Cross and Nova Ukraine, a US-based charity.
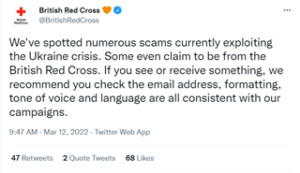
British Red Cross addressed the scam on Twitter.
Source: Twitter
Action Fraud, the UK’s national reporting centre for fraud and cybercrime, has received almost 200 reports of bogus requests to fundraise for victims of the war in Ukraine. Some criminals have even had the audacity to pretend to be Wladimir Klitschko, the brother of Kyiv’s mayor Vitali Klitschko.

Example of scams used by threat actors using Ukraine to lure people to part with their money.
Source: @CyberProtectUK
Check the basics before you donate
While all this might put anyone off making a donation, there’s really nothing to worry about if you adhere to some basic principles: check the charity’s logo, email address and website carefully first and only use their official channels. (You can check a charity’s name and registration number on the British government’s website, www.gov.uk. Almost all British charities with an annual income of £5,000 or more must be registered.) Don’t reply to emails that come out of the blue or click on any links within them. And if in any doubt at all, don’t donate unless you’re absolutely sure.
For more details about what you can do to keep yourself, your business and others safe from phishing scams, and what to do if you’ve already opened a malicious attachment or provided personal information, please do read ‘Phishing Scams in the Age of COVID-19: Avoid the Traps’.
If you would like to find out more about our full range of cyber security services for your organisation, please contact us via or our website. Alternatively, if you need urgent support you can contact the Quorum Cyber Incident Response Team for immediate assistance on +44 333 444 0041. Our dedicated team operates 24×7 to keep your organisation moving.















