Get in Touch
Zerobot targets multiple vulnerabilities
The term “Zerobot” in this article is not associated with, and should not be confused with, the commercial company zerobot.ai, their verbal chatbot product, Zerobot, nor any of the company’s other products or services.
Target Industry
Opportunistic targeting.
Overview
Severity level: High
First reported in mid-November, Zerobot is a new Golang (also known as Go) language-based malware that actively exploits at least 18 known vulnerabilities with possibly three more, but these have not yet been published. The likely aim of Zerobot it to assimilate compromised systems into the botnet for use in future distributed denial-of-service (DDOS) attacks.
Once initial compromise has been achieved via a common vulnerability and exposure (CVE), Zerobot will download further scripts for propagation. This download will be called from the Zerobot command and control (C2) server (176.65.137[.]5). The downloaded file is labeled as ‘Zero’, thereby offering simple yet effective malware identification.
Due to the programme being written in the Go language, Zerobot can be used against most systems using WindowsOS, MacOS, or Linux.
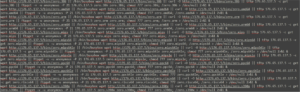
Figure 1: Zero script to enable propagation (Fortinet)
The following vulnerabilities are known to be used in target breaches:
– CVE-2014-08361: miniigd SOAP service in Realtek SDK
– CVE-2017-17106: Zivif PR115-204-P-RS webcams
– CVE-2017-17215: Huawei HG523 router
– CVE-2018-12613: phpMyAdmin
– CVE-2020-10987: Tenda AC15 AC1900 router
– CVE-2020-25506: D-Link DNS-320 NAS
– CVE-2021-35395: Realtek Jungle SDK
– CVE-2021-36260: Hikvision product
– CVE-2021-46422: Telesquare SDT-CW3B1 router
– CVE-2022-01388: F5 BIG-IP
– CVE-2022-22965: Spring MVC and Spring WebFlux (Spring4Shell)
– CVE-2022-25075: TOTOLink A3000RU router
– CVE-2022-26186: TOTOLink N600R router
– CVE-2022-26210: TOTOLink A830R router
– CVE-2022-30525: Zyxel USG Flex 100(W) firewall
– CVE-2022-34538: MEGApix IP cameras
– CVE-2022-37061: FLIX AX8 thermal sensor cameras
Once a system is infected with Zerobot, the malware awaits further command from its C2 network. These commands include:
– Ping – Heartbeat, maintaining the connection
– Attack – Launch attack for different protocols: TCP, UDP, TLS, HTTP, ICMP
– Stop – Stop attack
– Update – Install update and restart Zerobot
– Enable_scan – Scan for open ports and start spreading itself via exploit or SSH/Telnet cracker
– Disable_scan – Disable scanning
– Command – Running OS command, cmd on Windows and bash on Linux
– Kill – Kill botnet programme
Impact
Compromise via ZeroNet will provide the threat actor with an initial access point to the victim network and thereby enable the possibility for further malicious compromise.
Additionally, Zerobot will use an infected system to act on the threat actor’s behalf for future DDOS attacks.
Vulnerability Detection
Victim systems will highly likely be operating slower than usual due to the botnet using much of the available processing power. If the system is running slower than usual, check it for an exe. file labeled as ‘Zero’.
Up-to-date Endpoint Detection and Response (EDR) solutions such as Microsoft Defender will almost certainly detect intrusion attempts by botnet malware such as Zerobot and alert the user once detected.
Affected Products
WindowsOS, MacOS, and Linux.
The following architecture is targeted by Zerobot:
– i386
– amd64
– arm
– arm64
– mips
– mips64
– mips64le
– mipsle
– ppc64
– ppc64le
– riscv64
– s390x
Containment, Mitigations & Remediations
The implementation of an up-to-date EDR solution such as Defender is highly recommended to detect and halt malicious botnet malware before significant compromise can take place.
Furthermore, it is recommended that customers update all associated systems effected by the CVEs in the ‘Overview’ section. This will limit the threat landscape for potential threat actors targeting customer systems.
Indicators of Compromise
Associated Zerobot hashes:
– 6c284131a2f94659b254ac646050bc9a8104a15c8d5482877d615d874279b822
– 7ae80111746efa1444c6e687ea5608f33ea0e95d75b3c5071e358c4cccc9a6fc
– f0bb312eacde86d533c922b87e47b8536e819d7569baaec82b9a407c68084280
– b1d67f1cff723eda506a0a52102b261769da4eaf0551b10926c7c79a658061fd
– 7722abfb3c8d498eb473188c43db8abb812a3b87d786c9e8099774a320eaed39
– cd9bd2a6b3678b61f10bb6415fb37ea6b9934b9ec8bb15c39c543fd32e9be7bb
– df76ab8411ccca9f44d91301dc2f364217e4a5e4004597a261cf964a0cd09722
– 191ce97483781a2ea6325f5ffe092a0e975d612b4e1394ead683577f7857592f
– 2955dc2aec431e5db18ce8e20f2de565c6c1fb4779e73d38224437ac6a48a564
– 50d6c5351c6476ea53e3c0d850de47059db3827b9c4a6ab4d083dfffcbde3579
– 5af002f187ec661f5d274149975ddc43c9f20edd6af8e42b6626636549d2b203
– 9c16171d65935817afd6ba7ec85cd0931b4a1c3bafb2d96a897735ab8e80fd45
– e0766dcad977a0d8d0e6f3f58254b98098d6a97766ddac30b97d11c1c341f005
– 447f9ed6698f46d55d4671a30cf42303e0bd63fe8d09d14c730c5627f173174d
– 74f8a26eb324e65d1b71df9d0ed7b7587e99d85713c9d17c74318966f0bead0a
Associated Zerobot IP:
– 176.65.137[.]5
Threat Landscape
Zerobot exploits a multitude of vulnerabilities in order to gain initial access. The wide range of CVEs targeted is almost certainly designed to create a large target surface with many options of initial compromise. This tactic is likely to increase over time as it enables greater infection probability and complicates defensive actions.
Threat Group
Based on the wide array of CVEs targeted by the threat actor operating Zerobot, the group is likely to be advanced and well organised, making the threat of Zerobot more severe.
Mitre Methodologies
T1071.001 – Application Layer Protocol: Web Protocols
T1105 – Ingress Tool Transfer
T1190 – Exploit Public-Facing Application
T1489 – Service Stop
Further Information
Fortinet– Zerobot analysis
Security Week – Zerobot news article
Bleeping Computer – Zerobot news article

