Get in Touch
Please get in touch using the form below.
Energy sector targeted by Lazarus
Target Industry
Energy sector
Overview
Severity Level: High – Vulnerability could result in elevated privileges and significant data loss.
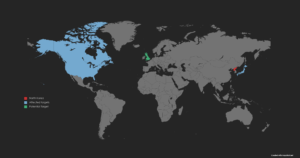
North Korean state-sponsored threat group Lazarus, also known as APT38, is exploiting a Log4J vulnerability found within VMware Horizons servers to targett energy providers’ networks in the United States, Canada and Japan.
The group is reportedly using multiple malware strains to further their goals in this latest wave of attacks. These include Vsingle, YamaBot and a recently developed remote access trojan (RAT), MagicRAT.
This report has been issued to highlight the dangers posed to the energy sector and how best to mitigate the emerging threat.
Impact
Lazarus have likely decided to target VMware Horizon due to the system running with heightened privileges. This enables the adversary to conduct steps to deploy malware covertly, such as deactivating Windows Defender via registry key modifications.
The three malware strains used by Lazarus in this latest surge of activity are:
Vsingle backdoor – Allows for advanced reconnaissance commands to steal network/account credentials, create admin roles, and to establish reverse shell connection with command and control (C2).
YamaBot – Written in the GO programming language (Golang), this malware can affect all major operating systems, and features multiple capabilities found in other RATs. Initial access is made via the issuing of exploitable HTTP requests.
Capabilities of YamaBot include:
- Downloading of files from a remote location
- Executing arbitrary commands on the endpoints
- Sending process information to C2
- Uninstalling itself when the designated task is complete to maintain covert posture
MagicRAT – Written in the C++ programming language, this malware targets a systems Qt framework by statically linking it to the RAT. Additionally, the RAT executes arbitrary commands to implement covert actions such as keylogging, screen capture, file management and self-uninstall when all directed tasks have been completed.
Vulnerability Detection
All three malware strains use escalated privileges to execute arbitrary commands, therefore increased activity that matches this parameter has a realistic possibility of being linked to Lazarus’s compromise. However, for a more defined detection capability, please see the IOC section below for additional compromise alerts.
Affected Products
VMware Horizons Servers.
Containment, Mitigations & Remediations
Network defence systems are advised to actively search for the provided indicators of compromise (IOCs), and action should be conducted to remove potentially hostile code when detected.
Additionally, VMware applications should be continuously updated to the latest patching level, to ensure that gaps in security are plugged at the earliest opportunity.
Indicators of Compromise
Vsingle – IOCs including hashes and associated domains can be found here.
YamaBot – Hash files:
f226086b5959eb96bd30dec0ffcbf0f09186cd11721507f416f1c39901addafb
6db57bbc2d07343dd6ceba0f53c73756af78f09fe1cb5ce8e8008e5e7242eae1
MagicRAT – IOCs including hashes, associated IPs and URLs can be found within this GitHub – MagicRAT IOC page.
Threat Landscape
Lazarus is a North Korean state-sponsored threat group that specialises in offensive financial cyber operations on behalf of the Reconnaissance General Bureau to help fund the nation’s government. Previous attacks have included the targeting of casinos, cryptocurrency exchanges, banks and the SWIFT system. Targeted attacks of Western finance and energy sector infrastructure for monitory and intellectual property (IP) gain will almost certainly continue for the foreseeable future based on the North Korean government’s requirement for additional unconventional funding, whilst international sanctions prevent regular cash-flow. The current energy crisis is likely fuelling further targeted ransomware exploitation based on perceived industry pressure to meet current demands.
Threat Group
Lazarus Group – APT38
APT38 ATT&CK Navigator
Mitre Methodologies
APT38 RAT Methodology
T1190 – Exploit Public-Facing Application
T1083 – File and Directory Discovery
T1590 – Gather Victim Network Information
T1003.005 – OS Credential Dumping: Cached Domain Credentials
T1136.002 – Create Account: Domain Account
T1543.003 – Create or Modify System Process: Windows Service
T1547.001 – Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder
T1053.005 – Scheduled Task/Job: Scheduled Task
T1560 – Archive Collected Data
T1518.001 – Software Discovery: Security Software Discovery
T1562.001 – Impair Defenses: Disable or Modify Tools
T1562 – Impair Defenses: Disable or Modify System Firewall
T1018 – Remote System Discovery
T1608 – Stage Capabilities: Upload Malware
Further Information
Talos Intelligence – Lazarus Exploits
Talos Intelligence – MagicRAT
Japan CERT – YamaBot Malware
Maldefence – Vsingle

